What is Cloud Security?
Cloud security refers to the policies, controls, procedures, and technologies that work together to protect cloud-based systems, data, and infrastructure. From securing data in transit to defending cloud applications against unauthorized access, cloud security encompasses a broad spectrum of practices designed to maintain data privacy, safeguard data integrity, and ensure access reliability.
The Scope of Cloud Security
At its core, cloud security is concerned with three fundamental aspects:
- Confidentiality: Ensuring that sensitive information is accessible only to authorized users.
- Integrity: Protecting data from being altered or tampered with by unauthorized individuals.
- Availability: Guaranteeing legitimate users’ reliable access to data and resources when needed.
- 1. What is Cloud Security?
- 2. Key Threats and Challenges in Cloud Environments
- 3. Cloud Security Solutions
- 4. Implementation of Cloud Security Solutions
- 5. Managed IT Service Providers: Enhancing Cloud Security
- 6. Regulatory Compliance and Cloud Security
- 7. Securing Your Future in the Cloud
- 8. Need Help Getting Started?
- 9. Related Articles
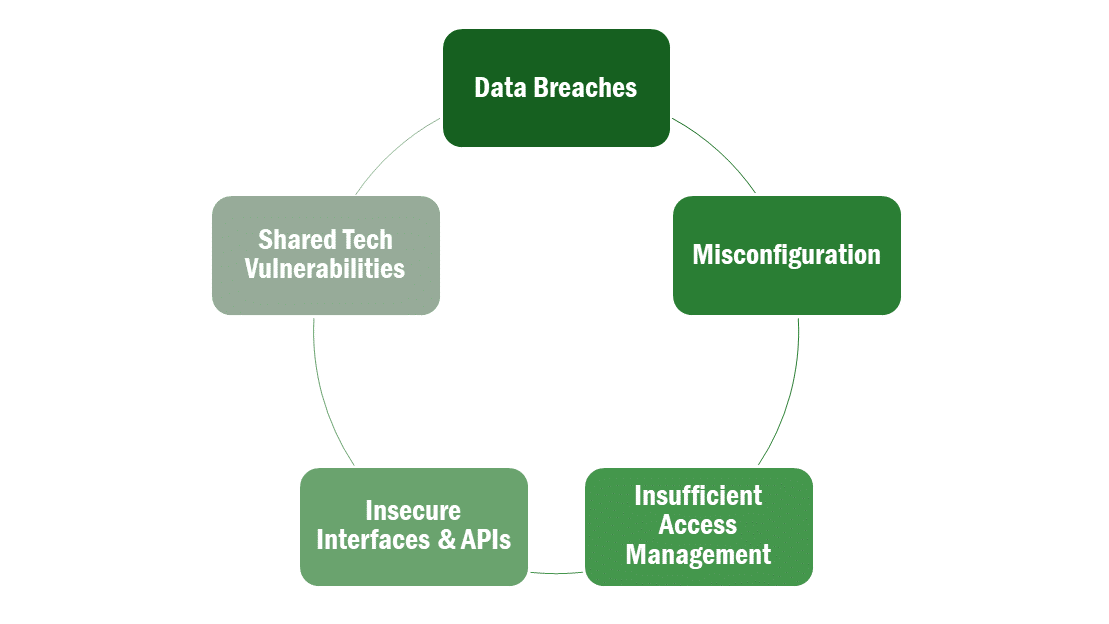
Key Threats and Challenges in Cloud Environments
Cloud environments face a unique set of security threats and challenges:
- Data Breaches: The most significant threat to cloud security is the risk of data breaches. Such incidents can expose sensitive customer data, trade secrets, and other valuable information to cybercriminals.
- Misconfiguration: Cloud environments are complex and can be difficult to configure correctly. Inadequate configurations can leave unintended openings for attackers.
- Insufficient Identity, Credential, and Access Management: Weak user authentication and inadequate access controls are frequent vulnerabilities that attackers exploit to gain unauthorized access to cloud systems.
- Insecure Interfaces and APIs: Cloud services are often accessed through APIs. If these interfaces are not secure, they can be a potential entry point for cyberattacks.
- Shared Technology Vulnerabilities: In a cloud environment, resources are shared among multiple users. A vulnerability in the shared infrastructure can affect all tenants.
By addressing these risks with comprehensive security measures, companies can protect data in the cloud and maintain the trust of their clients and partners. In the following sections, we will explore specific cloud security solutions and best practices to achieve this goal, emphasizing the role of managed IT service providers in enhancing cloud security capabilities.
Cloud Security Solutions
As organizations transition to cloud computing, they must employ robust cloud security solutions to safeguard their data and systems. These solutions vary widely, encompassing software, hardware, and strategic practices designed to protect cloud infrastructure and data from various threats. Here we discuss several critical solutions that form the backbone of effective cloud security.
Types of Cloud Security Solutions
- Encryption: Encryption is fundamental in securing data both at rest and in transit. By encoding data, encryption ensures that even if data is intercepted or accessed without authorization, it remains unreadable and secure.
- Identity and Access Management (IAM): IAM systems control who can access what resources within an organization. They enforce user authentication, authorize appropriate access levels based on user roles, and manage the credentials of all entities accessing the data.
- Intrusion Detection Systems (IDS) and Firewalls: These systems monitor network traffic for suspicious activity and known threats, acting as a shield against cyber-attacks. Firewalls serve as a barrier between secure internal networks and untrusted external networks, while IDS alerts administrators about potential security breaches.
- Antivirus and Anti-malware Software: This software is crucial for detecting, thwarting, and removing malicious software, which can be used to breach cloud systems.
Implementation of Cloud Security Solutions
Effective cloud security involves not only selecting the right tools but also implementing them strategically:
- Centralized Security Management: Utilizing a centralized security management platform can help streamline the monitoring and management of various security tools and systems, providing a unified view of security events.
- Regular Updates and Patch Management: Keep all cloud security software and systems up to date with the latest security patches and updates. This practice is vital in protecting against newly discovered vulnerabilities.
- Multi-Factor Authentication (MFA): Implementing MFA can add an additional layer of security, making it more challenging for attackers to gain access to cloud systems merely by compromising a single password.
Challenges in Implementation
Despite the availability of advanced security solutions, organizations often face challenges in implementation, such as:
- Complexity in Integration: Integrating new security solutions into existing cloud environments can be complex and may require considerable time and expertise.
- Skill Gaps: There may be a lack of necessary skills within the organization to effectively implement and manage cloud security solutions.
- Cost Constraints: While essential, some advanced security measures can be costly, making it difficult for smaller organizations to implement them without compromising other areas of their business.
Managed IT service providers play a crucial role in overcoming these challenges. They offer the expertise and resources necessary to implement comprehensive security solutions efficiently. In the next section, we will delve deeper into how these providers can enhance cloud security, particularly focusing on real-time monitoring, incident response, and compliance management.
Managed IT Service Providers: Enhancing Cloud Security
In today’s complex cybersecurity landscape, managed IT service providers (MSPs) are invaluable allies for businesses seeking to strengthen their cloud security. MSPs specialize in handling and securing IT infrastructures, offering a range of services that can significantly improve an organization’s ability to prevent, detect, and respond to security threats. Here’s how MSPs can bolster your cloud security.
Services Offered by Managed IT Service Providers
- Real-time Monitoring and Incident Response: MSPs provide 24/7 monitoring of your cloud environments, ensuring that any suspicious activity is detected and addressed promptly. This continuous surveillance helps prevent potential security breaches and minimizes downtime by quickly responding to incidents.
- Comprehensive Risk Assessments: Regular risk assessments are crucial for maintaining strong cloud security. MSPs conduct these assessments to identify vulnerabilities within your cloud infrastructure and recommend measures to mitigate these risks.
- Advanced Threat Detection and Management: Using sophisticated tools and technologies, MSPs can detect advanced threats that might bypass basic security measures. They also manage the lifecycle of such threats, from detection to remediation.
- Compliance and Governance: With extensive knowledge of regulatory requirements, MSPs ensure that your cloud solutions comply with laws and regulations such as The Health Insurance Portability and Accountability Act (HIPAA), or Payment Card Industry Data Security Standard (PCI-DSS). This is crucial for avoiding legal penalties and maintaining customer trust.
Selecting the Right Managed IT Service Provider
Choosing the right MSP is critical. Consider these factors when selecting an MSP to enhance your cloud security:
- Expertise and Experience: Look for providers with proven expertise in managing cloud security and a record of accomplishment in dealing with organizations of comparable size and industry like yours.
- Security Practices and Protocols: Evaluate the MSP’s own security practices. Ensure they have robust protocols in place and that they regularly update their security measures.
- Service Level Agreements (SLAs): SLAs are crucial for defining what services the MSP will provide and the expected levels of performance and responsiveness. Ensure these align with your security needs and organizational goals.

Benefits of Partnering with an MSP
Partnering with an MSP offers numerous benefits:
- Cost Efficiency: MSPs can provide a team of experts and advanced technologies at a fraction of the cost of maintaining such resources in-house.
- Scalability: As your business grows, MSPs can easily scale your security measures to meet increasing demands without requiring significant new investments from you.
- Expert Guidance: MSPs bring specialized knowledge and experience, providing you with insights and strategies that are at the forefront of cloud security.
Leveraging the services of a Managed IT service provider can significantly enhance your organization’s cloud security, providing not just protection but also strategic advice tailored to your specific needs.
Regulatory Compliance and Cloud Security
Navigating the complex regulatory landscape is a critical aspect of cloud security. Compliance is not merely a legal obligation but also a cornerstone of trust and reliability in business operations. Here, we will explore the key regulations affecting cloud security and how organizations can ensure compliance through effective security measures.
Overview of Relevant Regulations
Many industries, especially those handling sensitive information like healthcare and finance, are subject to strict regulatory requirements concerning data security and privacy. Key regulations include:
- Health Insurance Portability and Accountability Act (HIPAA): HIPAA in the United States mandates that healthcare providers implement robust security measures to safeguard patient data. This regulation is essential for any entity within the healthcare sector, including doctors, hospitals, insurance companies, and other healthcare providers. It ensures the confidentiality, integrity, and availability of protected health information (PHI) and provides patients with certain rights over their information. Non-compliance can result in significant penalties, emphasizing the importance of data privacy and security in healthcare.
- Payment Card Industry Data Security Standard (PCI DSS): PCI DSS is a set of security standards designed to ensure that all businesses that accept, process, store or transmit credit card information maintain a secure environment. This standard is crucial for any business dealing with credit card data, as it helps protect cardholder data from theft and misuse. It impacts every organization that processes, stores, or transmits such data, reinforcing the importance of data security in today’s digital business landscape. Compliance with this standard is not only a requirement but also a responsibility to protect customer information.
Ensuring Compliance Through Cloud Security Measures
To meet these and other regulatory requirements, organizations must implement a range of cloud security measures:
- Data Encryption: Encrypting data both at rest and in transit is often a requirement under regulations like HIPAA. It ensures that sensitive information remains unreadable even if unauthorized access occurs.
- Access Controls: Implementing robust access controls ensures that only authorized personnel have access to sensitive data, a key compliance requirement across many regulations.
- Audit Trails: Maintaining comprehensive logs of data access and system changes helps organizations monitor compliance and provides evidence of compliance during audits.
- Data Sovereignty: Understanding and complying with data sovereignty laws that dictate where data can be stored and processed is crucial, especially for multinational organizations.
Challenges in Achieving Compliance
Achieving compliance in the cloud can be challenging due to:
- Evolving Regulations: Regulatory frameworks are constantly evolving, requiring organizations to stay informed and agile in their compliance efforts.
- Multi-Cloud Environments: Using multiple cloud services can complicate compliance, as each platform may have different security controls and standards.
- Vendor Management: Ensuring that cloud service providers comply with relevant regulations is crucial but can be challenging, given the complexity of cloud environments.
Role of Managed IT Service Providers in Compliance
Managed IT service providers can be instrumental in helping organizations navigate these challenges. They offer expertise in regulatory compliance specific to various industries and can assist in implementing the necessary security measures. Additionally, they can manage relationships with cloud vendors to ensure compliance across all services.
Maintaining compliance in cloud security is an ongoing process. This involves understanding regulatory requirements, implementing appropriate security measures, and continually monitoring and adapting to new regulations. With the help of knowledgeable partners like Managed IT service providers, organizations can not only meet these requirements but also strengthen their security posture and protect their valuable data.

Securing Your Future in the Cloud
Cloud security is an essential component of modern business operations, protecting sensitive data and ensuring compliance with stringent regulatory standards. Employing robust cloud security measures is not merely about defense but also about enabling your business to thrive and innovate securely in a digital-first world.
At thirtyone3 technology, we understand the complexities and challenges of securing cloud environments in healthcare. Our expertise in IT consulting and management services allows us to provide tailored solutions that not only meet regulatory requirements but also align with your strategic business objectives.
Our goal is to empower your organization to harness the full potential of cloud technologies safely and effectively. For more information on how we can assist with your cloud security needs or to schedule a consultation, please fill out our contact form or contact us at 623.850.5392.
Let us help you secure your cloud environment and ensure your data’s integrity and confidentiality. By adopting these comprehensive cloud security strategies and partnering with seasoned professionals, you can confidently navigate the complexities of the cloud, ensuring that your company’s data is protected against the evolving landscape of cyber threats.

